Basic Heap Exploitation: House of Force
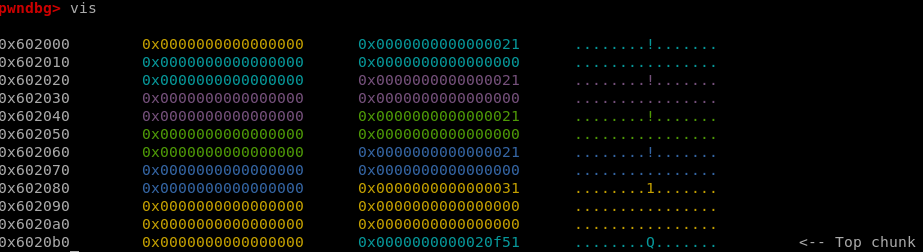
I recently finished a course on Linux heap exploitation, aimed to teach how the heap works and some popular exploitation techniques that are possible to execute once you are familiar with the heap’s metadata. In this short article, I will try to showcase some of the things that I have learned, with some examples.
Python Hash Tables Under the Hood

Are you a Python developer eager to learn more about the internals of the language, and to better understand how Python hash tables and data structures work? Or maybe you are experienced in other programming languages and want to understand how and where hash tables are implemented in Python? You’ve come to the right place!
ROP Emporium Ret2CSU Writeup
Last ROP Emporium callenge - Ret2CSU! This challenge requires a usage of something called Universal Gadget, that will allow us to use three parameters to functions calls, when we do not have any useful gadgets available to us. Our goal is to call the
ret2win function with rdx filled with 0xdeadcafebabebeef. As mentioned before, the main challenge here is having no gadgets allowing us to directly control rdx.
ROP Emporium Pivot Writeup
ROP Emporium callenge - Pivot! This challenge, as most ROP Emporium challenges, requires us to overflow the stack to reach the
ret2win function. In order to achieve this, we are going to need to create a stack pivot since there is not enough room in the stack itself.
Awesome Python modules you probably aren’t using (but should be)
Python is a beautiful language, and it contains many modules that aim to help us write better code. Here are some lesser-known ones.